| Email Address sales@sprintsmsservice.com |
Destination For Your Business Goal
| |
As we look toward , one thing is certain: No character is safe. The raw scans will tell the truth first, and whether you read them immediately or wait for the translation, the sheer chaos awaiting in the next chapter will be worth the anticipation.
Are you caught up? What are your theories for Chapter 281? Share in the discussion forums below! satanophany raw chapter 280 read next chapter 281 new
For those who cannot wait for the official translation, the release of the raw scans is a weekly pilgrimage. Here is your complete breakdown of what happened in Chapter 280, the state of the narrative, and—most importantly—how to prepare for . The Fallout of Chapter 279: Setting the Stage for 280 Before diving into the raw chaos of 280, a quick recap is essential. The previous chapters have seen the climax of the "Tokyo Annihilation Arc." Our protagonist, Yukina, and her fractured army of "Witches" have been locked in a brutal tug-of-war against the mysterious and grotesque "Disciples of the Serpent." As we look toward , one thing is
The dark, psychological, and action-packed world of Satanophany (often stylized as SANCTIFY ) has never been for the faint of heart. Created by the dynamic duo of writer Osamu Yamamoto and artist Masahiro Shibata, this manga has cultivated a dedicated cult following due to its unflinching portrayal of revenge, body horror, and psychological warfare. As of the latest releases, the community is buzzing with one singular focus: Satanophany Raw Chapter 280 . What are your theories for Chapter 281
Upon accessing the scans (currently circulating on Japanese aggregate sites and the weekly Young Magazine release), readers witnessed a non-stop adrenaline rush. Here are the three major beats: 1. The Birth of a New Enemy The chapter opens not with Yukina, but deep beneath the Tokyo Metropolitan Government building. A vial of "Original Sin"—a macguffin teased since Chapter 100—shatters. From the ooze emerges a creature that is neither human nor demon. Dubbed by raw readers as "Adamus," this entity absorbs General Kurokami’s arm and instantly unlocks the ability to negate Witch contracts. This is a game-changer. For the first time, a Witch’s immortality is rendered useless. 2. Yukina vs. The Mental Collapse Chapter 280 dedicates six visceral pages to Yukina’s internal struggle. After her forced evolution in 279, she is now hearing the voice of "The Serpent Father." The raw dialogue (translated by fans) suggests that the source of the Witches’ power is actually a parasitic alien entity. Yukina must choose: give in to the parasite and gain enough power to destroy Adamus, or retain her soul and risk everyone she loves. She chooses a terrifying third option: partial transformation . 3. The Return of Ohara In a shocking twist, the seemingly dead detective Ohara (presumed killed in Chapter 250) crashes a military helicopter into the spawning Adamus. Severely scarred and missing an eye, Ohara reveals he made a back-alley contract with a rogue, low-level demon. He is no longer a human ally—he is a vengeful phantom with only 24 hours to live. His goal? Kill everyone: Witches and Disciples alike.

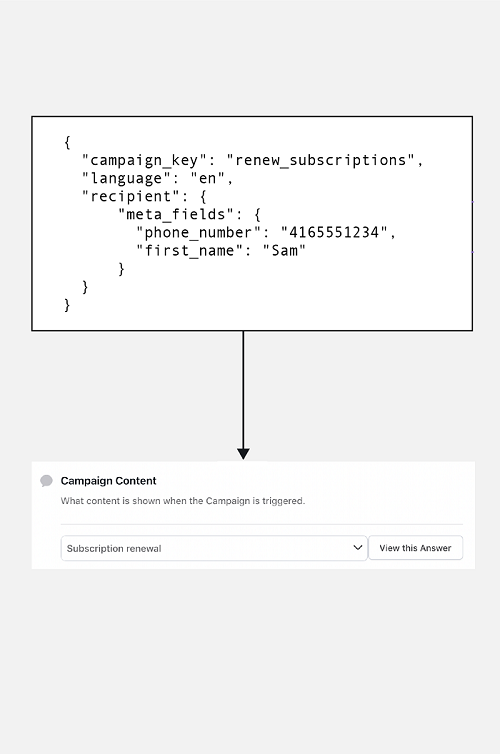
Personalized Messaging
Flexible personalized messaging with editable fields for you to send SMS conviniently.

Language-Based Messaging
Create a customized message in your preferred language and send it in unicode.

Two-Factor Authentication
Secure your applications at scale by sending dynamic verification codes.

Scheduling & Group SMS
Strategically manage your marketing based on the preferences.

Global and Instant Delivery
Send your SMS all across the globe hassle-free and instantly.

Multiple Interface Options
Choose how to send a message using our SMS Panel, API or SMPP.
SMS API can be considered safe if proper security measures and protocols are implemented. Here are three pointers that show the safety features of SMS API:
Encryption
Encryption is one of the key security features of SMS API. It ensures that the data being transmitted between different software components is protected from unauthorized access, interception, or modification. APIs should use industry-standard encryption algorithms, such as SSL or TLS, to encrypt data in transit and protect sensitive information.
Authentication and authorization
SMS API should also implement strong authentication and authorization mechanisms to ensure that only authorized users and applications can access and use the API. This can be achieved through methods such as API keys, OAuth tokens, or multi-factor authentication, which help to verify the identity of the user or application and prevent unauthorized access.
Compliance and auditing
SMS API should comply with relevant industry standards, regulations, and best practices, such as PCI DSS, HIPAA, or GDPR, to ensure that the API is secure and compliant with data protection laws. Regular auditing and monitoring of the API usage can help identify potential security vulnerabilities or incidents and take appropriate actions to mitigate them.
Java SMS API
Java SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in Java. Java SMS API supports various protocols such as SMPP, HTTP, and FTP, and is widely used in enterprise-level messaging applications.
Python SMS API
Python SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in Python. Python SMS API supports various protocols such as SMPP, HTTP, and FTP, and is popular for its ease of use and readability.
PHP SMS API
PHP SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in PHP. PHP SMS API supports various protocols such as SMPP, HTTP, and FTP, and is widely used in web development.
Ruby SMS API
Ruby SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in Ruby. Ruby SMS API supports various protocols such as SMPP, HTTP, and FTP, and is popular for its simplicity and expressiveness.
.NET SMS API
.NET SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in .NET languages such as C# and Visual Basic. .NET SMS API supports various protocols such as SMPP, HTTP, and FTP.
Node.js SMS API
Node.js SMS API is a set of programming tools and libraries that developers can use to build SMS messaging applications in Node.js, a popular JavaScript runtime. Node.js SMS API supports various protocols and is known for its speed and scalability.
SMS APIs are commonly used by businesses and organizations for a variety of purposes. One popular use case is marketing and promotions, where SMS messages are used to send marketing campaigns, special offers, and event reminders to customers. Another use case is authentication and security, where SMS messages are used for two-factor authentication to help prevent unauthorized access and reduce the risk of fraud. Finally, SMS APIs are also used for notifications and alerts, such as appointment reminders, payment confirmations, and delivery notifications, to improve communication and enhance the overall customer experience.
Marketing and promotions
SMS APIs are commonly used by businesses to send promotional messages to their customers. This can include marketing campaigns, special offers, and reminders about upcoming events or promotions. It is a boon in disguise for small and medium enterprise.
Authentication and security
SMS APIs can be used for two-factor authentication, which adds an extra layer of security to the login process by requiring users to enter a code that is sent to their mobile phone via SMS. This can help prevent unauthorized access and reduce the risk of fraud.
Notifications and alerts
SMS APIs can be used to send notifications and alerts to customers or employees, such as appointment reminders, payment confirmations, or delivery notifications. This can help improve communication and reduce the risk of missed appointments or deadlines.
SMS APIs are difficult to integrate with existing systems. In reality, most SMS APIs are designed to be easy to integrate with existing systems, and many providers offer extensive documentation and support to help developers get started.
SMS APIs are only for large organizations. While SMS APIs are certainly useful for large organizations with a large customer base, they can also be beneficial for smaller businesses or organizations that need to communicate with customers or employees quickly and reliably.
SMS APIs are expensive. While some SMS API providers may charge high fees, there are many providers that offer affordable pricing plans and flexible payment options, making SMS APIs accessible to businesses and organizations of all sizes.
SMS APIs are not secure. In reality, most SMS APIs use encryption and other security measures to ensure the confidentiality and integrity of messages sent over the API. Additionally, many SMS API providers offer additional security features such as two-factor authentication to further enhance security.